The second season of Mr. Robot has just finished last week. While it’s one of the most amazing thing I’ve ever seen, it is also held as the TV show with the closest depiction how computer hacking works for real (see for example Quora or Reddit). Looks like it inspired a lot of people to “try out” the tools the characters use on the show (adding to the popularity of Kali Linux, or the Wickr chat app for example), which does feel a natural way to relate to your favorite characters, in a geek way.
I couldn’t resist either, and tried to dig a bit deeper, learning some geek (ie. not professional) lessons about how hacking works, party from the events in the show directly, partly by following for a few steps what were done in the show, and deconstructing the results. Here’s what I’ve collected so far:
Social engineering is likely a big part, a crucial enabler of most “successful” hacks. The show works with characters so it might be biased towards human actions, but it makes sense that social engineering can open door where the “bits” are closed. All the shows main hacks I remember included social engineering (not going to spoil here anything). This also made me a lot more aware in life, for example when talking with my bank online, or trying to get official things done in a way that it involves trust. Very much seems to me, that social engineering vulnerabilities and “opportunities” are really abound, and that makes me a lot more careful. For example, when calling to the bank, my verification data is three pieces of information that is available online or relatively easy, and I think of how I’ve seen such situation abused (in fiction, mind you), then I get a little jumpy. Not sure how other countries are like, but it feels like so many weak points in Taiwan, that she is just protected by the language barrier from western hackers/scammers – but sure that doesn’t deter another hostile nation. So yeah, my lessons is trying to improve on things, be mindful of trust-based situations encountered, while do be more confident to get things done better (in a non-malicious way of course), as confidence is one of the key ingredients of social engineering as well.
Watching some BlackHat videos, and reading online, some people say they can hack anything they want. I’m pretty confident, that doesn’t mean that exactly, but that the people with knowhow will find some way to figure things out in the end. In my (probably simplistic) view, though, it’s often the case that things that people think can be hacked easily are actually hard, while things they think cannot be hacked is actually quite doable. This comes down to the fact that professionals and outsiders (in any field) have a different view of difficulty and ease.
Most hacking takes a lot of time. It came up on the show was well, the “naive” character waiting for thing to happen right way, while the professional knows that some things doesn’t work that way. Case to point, for testing purposes, I tried out a tool to recover the wifi network password from a WEP-enabled access point I had around: yeah, “progress is made” almost immediately, and then still going on 2 hours later, and 6 hours later, and finally got a “result” the next morning. Worked, but boy does it need patience. I’d think the same applies for all kind of surveillance, and many “tricks” from social engineering, so definitely appreciate, that patience is a big virtue.
Many hacks have hardware components, and they are more accessible now than ever. It can be as simple as a Pringles cantenna. Or intermediate such as a single board computer (think Raspberry Pi, and similar) or microcontroller (think Arduino, and similar) interfacing with some sort of target hardware. Or something even more complex such as an entire board-sensors-analytics-response package to carry out something larger (such as a bundle like this for counter-surveillance). Every level is now more accessible to people, as hardware is cheaper than ever before, knowledge of tools is more open, and both software and hardware is capable of doing a lot more. So I guess one advice is, be wary of unknown hardware you come across!
Encryption is everywhere, and it’s now easier to use than ever. Would highly recommend to use it to get a much better peace of mind, something that works even for people too who are not really threatened. Full disk encryption (dm-crypt), local encrypted storage to keep your “valuables” (veracrypt), smartphone full disk/SD card encryption. All should help to counter possible data loss, something that’s becoming a problem more and more. Of course, forgetting your password will make you lose access to the data (happened to me), so caution is advised, but it’s worth it.
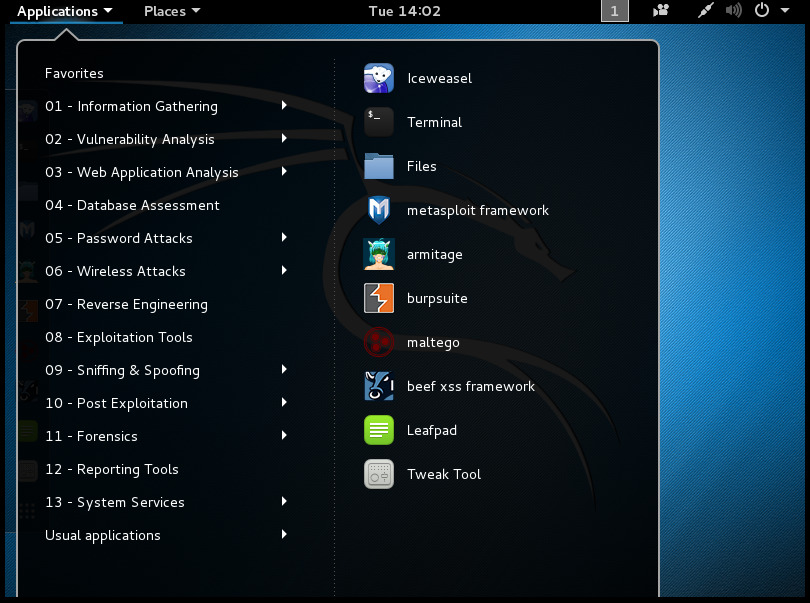
Most hacks need specialists. To successfully own a system, most of the time one has to know it inside out (the rest of the time it’s just luck), so people have to choose what knowledge they specialize in. No hacker knows all the tricks, and most hacks need a combo of tricks to work (low hanging fruit doesn’t stay for long in the wild to be exploited). There are also just so many tools, that one’s unlikely to be an expert in all. Kali Linux’s for example organizes tools it ships with into 12 categories, and each has about a dozen different software within. Many of those tools are themselves a collection of different pieces, so the variety is even larger. It needs a team of specialists coming together to cover all the bases. That’s how it worked out in Mr. Robot too, team, specialization, and lots and lots of co-ordination. This is of course also somewhat of a weak spot: more people involved means more chance for things to go wrong, as well as the better you are at something, the more likely you are calling attention to yourself.
Connected to the previous note, there are a lot of tools indeed, most of them looks something “shiney”/tempting with its promise of knowledge or power. And still you don’t need most tools, but can find some that works for your non-hack interests. One example was playing with Maltego CaseFile, which is also included in Kali Linux, and tickles my long-standing interest in “how should we organize knowledge”? I’ll be using it for complex “network”-type knowledge mapping in the future for sure. And, no real spoiler here, the FPI is using something similar to map the connections within fsociety. ;) Other example would be how people argue about the choices of text editors within the show. The smart (imho) answer is, that it does not matter, let tools be tools, and chose the best one for the task – just as much in other parts of life besides hacking too.
Likely everyone is wiretapped, but most of us don’t have anything that’s worth to overhear (at least that’s what people think). Bring social engineering into the picture, and the situation changes, “worthless” info can be now very valuable in a different context, someone carrying out a confidence trick either on you, or using your info. There are many tools to decrease exposure, but that’s a lot of work, and the payoff is still not as much for most people. (Especially when sharing so much voluntarily, both about ourselves, and about our conversations, in public). It needs building a habit, and I’d guess it’s never too early. Plenty of the story in Mr. Robot was also about how to overhear things, or deploying countermeasures against that.
Knowing that everyone is wiretapped or targeted some way, it’s really worth being paranoid about misdirection. Be mindful if something is off, when your information can leak, when strange things happen around you. I call it “cross-checking” myself, see if things make sense. In Mr. Robot the more knowledgeable characters often look at a situation and ask: “what does this mean, is there anything off here?” Doesn’t need much time or effort, but needs consistency. Also worth knowing when such a misdirection/threat is coming, for example knowing whether you’ve been pwned.
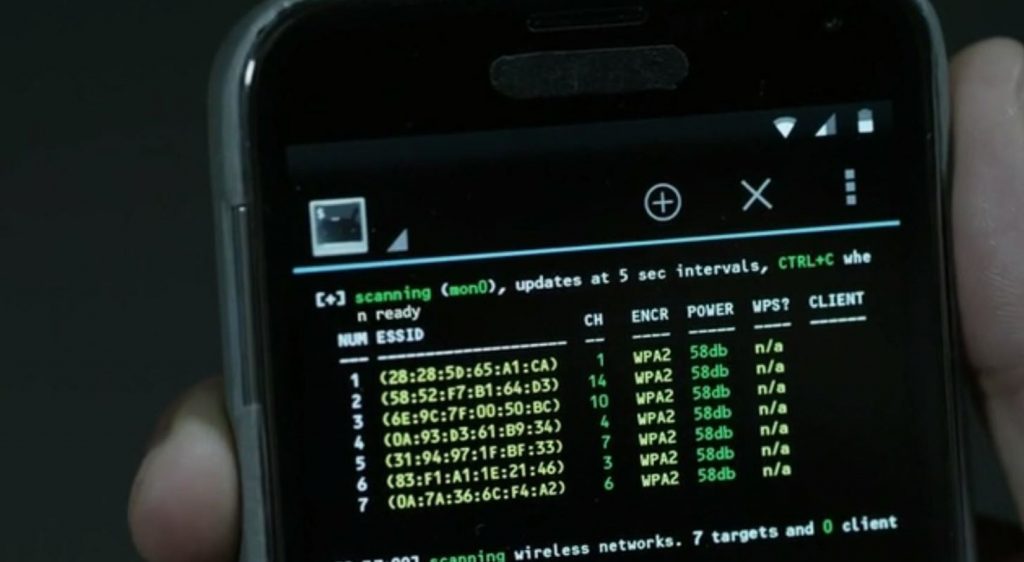
Lot of hacking causes disturbance, and that’s a weak point, something that might can be noticed by consistent cross checking. This needs to be taken into account when someone’s hacking (not to trigger the people’s or the system’s “alarm bells”), but also something to protect you against hacking, seeing the early signs of an attack. For example, I was also trying out recovering the password of a WPA encrypted wifi access point at home. The technique relies on disconnecting a connected client with fake data, and then listening how it tries to reconnect. From overhearing that connection the attacker can infer little pieces of the secret shared between the access point and the device, eventually recovering the password (if I understand it correctly). When I tried this between my smartphone and wifi router, it took a long time, and the phone’s internet connection was pretty unusable, the disconnection/reconnection was very visible. If you are hacking, you don’t want to be visible. On the other side, seeing something unusual can tip you off whether you are being targeted.
So big part of life can now be done over computers, creating a lot of opportunities for better living, but also opportunities for adversaries to target you from afar. That’s what creates cyber warfare, when the battleground is within the computers (the copper, the fibers, the chips), wherever they are around the world (or even in space, thanks to satellites:). Lots of things that were impossible before are possible now, and people’s thinking often doesn’t take that into account yet.
And finally, if you are hacking, you will always leave a trace. No matter what do you do, whether it’s locally or in the distance, it will leave a trace, and for most people, that won’t end well (so don’t be stupid!). For the actual professionals, I guess the trick is to have a trace that is benign, misleading, or falsified. If I remember my games of Uplink correctly, often the lack of trace is a larger giveaway, than having something misleading. In Mr. Robot, the characters (the hackers) are mostly in two camps, I think: some of them think they are doing a good job erasing their traces but they aren’t, others know they cannot hide everything so they mitigate the adverse effect of the traces left behind.
Well, that’s what I’ve picked up so far, and I’m sure professionals would pull their hair out seeing the ramblings of a sort-of wannabe hacker (not really, just a curious geek). So don’t mind me (though feel free to correct me) if I’m wrong about anything above! And definitely looking forward to the next season of Mr. Robot. :)


One reply on “I’ve learned this about hacking, inspired by Mr. Robot”
Great summary and observations about the show and hacking.