Doing software engineering (well-ish) is pretty hard to imagine without working in version control, which most of the time means git. In a practical setup of git there’s the question of how do I get access to the code it stores — how do I “check things out”? — and optionally how can others verify that it was indeed me who did the changes — how do I “sign” my commits? Recently I’ve changed my mind about what’s a good combination for these two aspects, and what tools am I using to do them.
Access Options
In broad terms git repositories can be checked out either though the HTTP protocol, or through the SSH protocol. Both have pros and cons.
Having two-factor authentication (2FA) made the HTTP access more secure but also more setup (no more direct username/password usage, rather needing to create extra access keys used in place of passwords). Credentials were still in plain text (as far as I know) on the machine in some git config files.
The SSH setup was in some sense more practical one (creating keys on your own machine, and just passing in the public key portion), though there were still secrets in plain text on my machine (as I don’t think the majority of people used password-protected SSH keys, due to their user experience). This is what I’ve used for years: add a new SSH key for a new machine that I’m working on, check code out through ssh+git, and work away.
When I’ve recently came across the git-credential-manager tool that supposed to make HTTP access nicer (for various git servers and services), and get rid of plain text secrets. Of course this is not the first or only one of the tools that does git credentials, but being made by GitHub, it had some more clout. This made me re-evaulate what options do I have for SSH as well for similar security improvements.
Thus I’ve found that both 1Password and KeePassXC (the two main password managers I use) have ssh-agent integration, and thus can store SSH keys + give access to them as needed. No more plain text (or password protected) private keys on disk with these either!
Now it seems there are two good, new options to evaulate, and for the full picture I looked at how the code signing options work in this context as well.
Code Signing Options
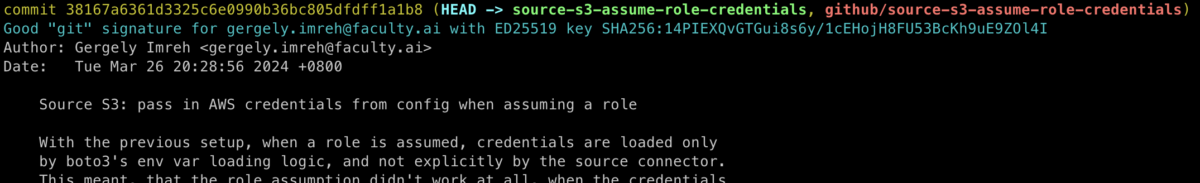
When signing my commits to authenticate authorship, it’s possible to use PGP/GPG (the “classic way”), or now also SSH keys (as detailed, for example here or here).
The GPG setup is well established, and also links my commits to my identities used elsewhere (e.g. signed emails sent to mailing lists that care about it, with the key linked from this site’s frontpage). This of course is not always needed or desired, but it decouples the identity from the code hosting platform. There’s some serious downsides as well, though: GPG signing keys are not supposed to be numerous (just a single one), and thus if I use multiple machines to work on, I will have to take my private keys with me between machines, for example making copies of them. Or if not making copies, then have them on hardware keys (that have other problems with backups and all that, if I got it right the last time I tried to understand the process).
The SSH key commit signing is much newer (need git version at least 2.34), but it’s also simpler: add a key to my git hosting service, sign commits with that key, and thus the service can match things up and show that match. I can add as many keys as machines I’m working on if needed, no need to transfer or copy keys between machines, and I can also choose use some keys for login only or code signing only.
A third party trying to verify these signatures, though, would need to get the keys from the hosting service (I’d find it surprising if people would distribute their commit signing keys out of band the same way as they do with GPG public keys, since there are likely more of them). Hence it git hosting services will need to make the user’s keys available (as they do at the relevant username.keys URLs, e.g. mine on GitHub and GitLab).
Also can’t forget to add the relevant keys to the list of allowed signing keys locally, and all the other relevant setup (see e.g. the GitHub and GitLab docs). There are a bit too many places to update, but it’s mostly set-it-and-forget-it. After that, once started to sign commits, adding the --show-signatures flag to the commands that support it (git log, git show for example), should show the signatures.
My Winning Combo
Looking at the opions above, there’s a matrix of options that we can use, and here’s what I think about them:
| GPG signature | SSH key signature | |
| Git Credential Helper | Extra setup | Simpler |
| SSH clone | The usual | Most convenience 👍 |
Really, where I want to be is just SSH keys for everything, even if they are imperfect, but they have the most number of puzzle pieces to fit.
SSH Key Security
While previously SSH keys were really just held as files in your ~/.ssh folder, most likely, recently I’ve found (tada!) that the password managers I use can also store & serve SSH keys: see in particular 1Password’s SSH documentation and KeePassXC docs (scroll to SSH Agent Integration on that page), though I’m sure other password managers can do this too.
1Password
The two password managers listed above handle things quite similarly. 1Password is a bit less hands-on, though, the default settings work pretty well.
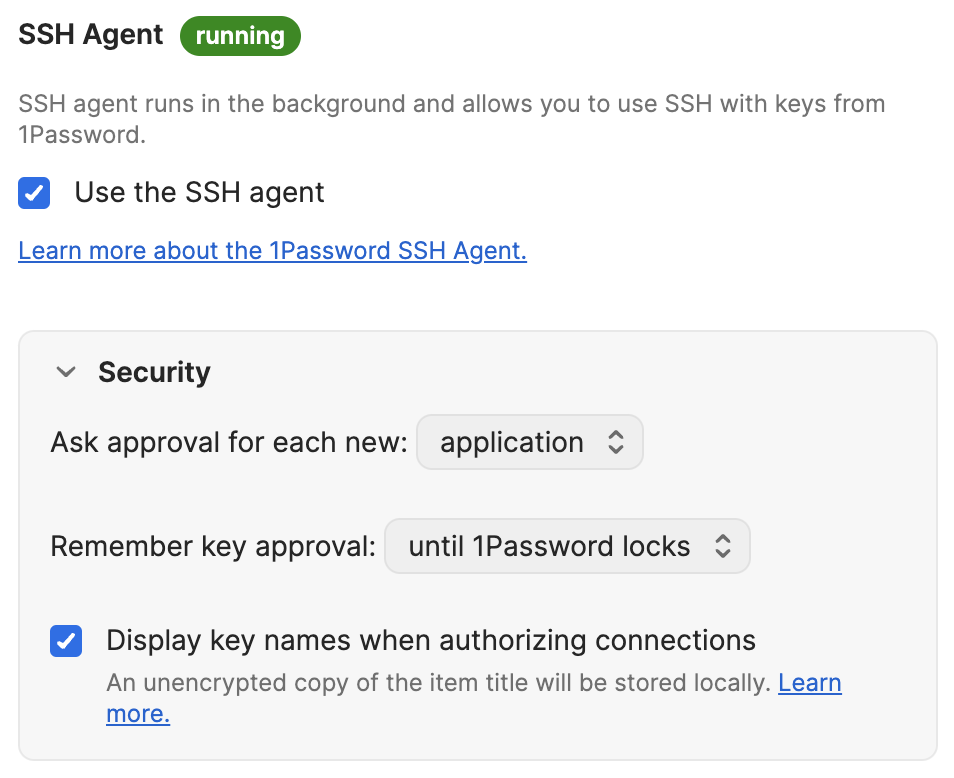
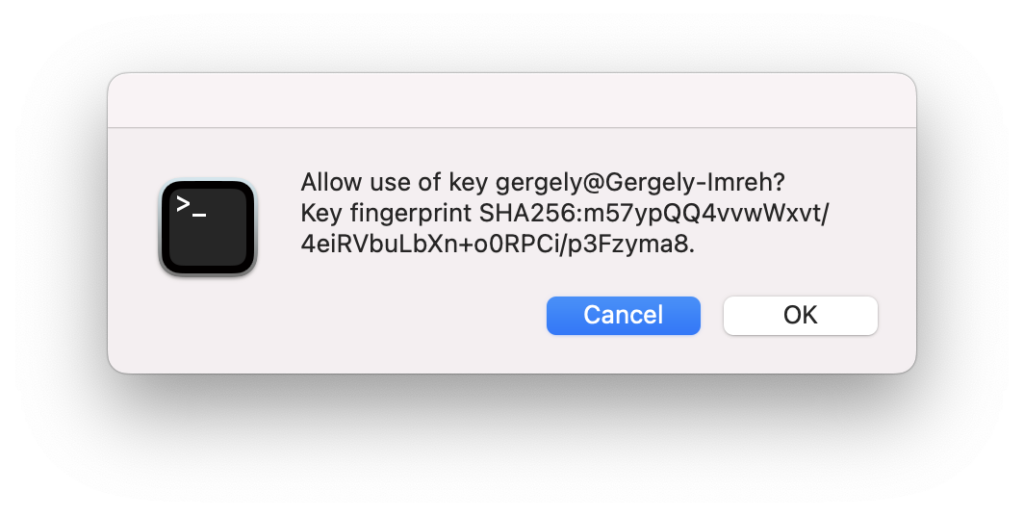
One important bit is that 1Password runs its own SSH agent, so that has to be configured in the relevant places, but it’s easy enough. The approvals are also useful, so it’s more transparent when something accesses the key.
With this things generally work, and relatively easy to reason about things. When things are less clear, it might be just a debug check-away away from seeing the keys added to this alternate agent:
$ export SSH_AUTH_SOCK=~/Library/Group\ Containers/2BUA8C4S2C.com.1password/t/agent.sock
$ ssh-add -l
256 SHA256:XfRsbxRMm+CN[...snip...]KeePassXC
KeePassXC, being open source, is my preferred solution of the two, though unsurprisingly it’s the more awkward one to set up. The main differences from 1Password include:
- needing to generate the keys externally to the password manager (rather than having built-in ssh keygen) – this is a con on usability but a strong pro on basing security on the established tool, rather than potentially questionably reimplement it
- uses the main SSH agent, so no extra setup is necessary in most of the tools – this is a potential pro on usability for configurations, but a potential con that the worflow and config of loading keys into the agent needs a bit more understanding to be both ergonomic and safe to one’s level of paranoia
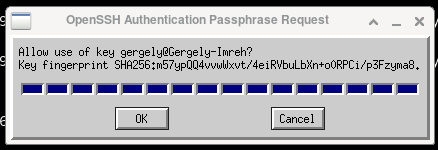
- the key use confirmation defaults to “ok” on pressing Enter on the pop-up (rather than Cancel) – this is a pro on usability, but con on “failing open” rather than closed
It’s still a pretty simple workflow, and it’s quite interesting to see how many things KeePassXC learned to do as well.
Experience
Thinking about the various threat models to my SSH crendentials, this setup adds one more layer to the defence in depth, and it does feel more relaxed already (relaxed from a point of stress I didn’t quite know I had before).
Picking the SSH key based login and signing feels like using the most appropriate tech for the moment, and there are still knobs for people to adapt it to their security levels (different SSH keys for login and signing, passwords on the keys themselves, etc…)
This setup works very well when I want to be notified whenever a tool’s using the SSH key so it would be more obvious if a stray process is trying, say exiltrate the keys. On the other hand this breaks down when git itself is running background processes, such as git-maintenance, so that’s not something that I could use here. So far out of (literally) thousands of codebases & repos I’ve used that maintenance setup exactly once, for convenience. For me it is not a major loss, then.
The one bit that feels a step backwards is that having the SSH keys in the password manager and carrying it around counteracts the “separate key for each system” arrangement. This might just be part of getting used to new processes, and not an actual downside.
Further Thoughts
In cybersecurity yesterday’s best practices might be inadecvate today and “last week’s” practices might be outright dangerous… Gonna keep revisiting this setup more broadly and in terms of details, as I learn more.
It’s a good question why even do code signing (besides having a “verified” check mark, which alone doesn’t mean much if not part of a verification process), though this needs some more space to unpack. For the time being I’ll assume that signing is better than not signing, if nothing else than as a forward looking prep for better audit processes down the line.
There’s really a question around having too many things in a single password manager: nowadays it can be the complete “royal flush” of password, TOTP, SSH key, recovery codes, passkey… and likely more bits that I might not be using yet? This does make me uneasy, and likely a scale on which usability and security will adjust over time (such as. bundling and unbundling various cybersecurity aspects).
I might also actually misunderstand various things above, if so, I’d be very keen to hear, just drop me a line!
Edit (2024-09-15): Looks like MacOS 14.6 Sonoma changes have broken the KeePassXC behaviour when confirmation is requested before using the key. I was looking at the workaround posted (some manual reconfiguring of ssh-askpass, but it seems pretty fragile… So I’d probably keep to 1Password on MacOS (sigh), while on Linux Bob continues to be your uncle…
2 replies on “Git login and commit signing with security”
@gergely
I recently became aware that I could sign commits. Bice that I could use the sshkey and make a linkage to my account on codeberg probably.
Btw, I use keepassxc as my secretservice and really like it. Switched over to it after dropping gnome. Only thing I never managed to get accomplished is that pam uses the password entered to decrypt my boot drive to unlock keepassxc.
Yeah, it’s encryption all the way down! :D Glad it works for you!
I probably wouldn’t tie different kinds of objects together in how are they en-/decrypted, just in case something goes wrong in the chain and leaves you high-and-dry…